

The article examines RFID (Radio Frequency Identification) technology, which is a common contactless radio tag technology used in various applications such as intercoms, bank cards, public transport tickets, office passes, pet tracking, toll collection and more . The article discusses in detail the two main types of RFID tags: low-frequency (125 kHz) and high-frequency (13.56 MHz), highlighting their differences in range, security and applications.
RFID is contactless radio tag technology. This is quite common and you can see it in many places: intercoms, bank cards, public transport passes, office passes, they are used to track pets, collect tolls, etc. The two main types of RFID tags are high frequency. and low frequency.
Low-frequency tags (125 kHz) – operate at a higher range. Despite the fact that they are dangerous and stupid, they are still used in primitive access control systems: in intercoms, offices, sports facilities, museums.
High-frequency tags (13.56 MHz) – have a lower effective range compared to low-frequency tags, but have more complex protocols. They support encryption, authentication and cryptography. These tags are commonly used in contactless bank cards, to pay for public transport and in high-security access control systems.
Here we will compare these two types of tags, look at the main protocols and learn how to work with them using Flipper Zero – we will read, emulate, save and clone them. You’ll see how you can store your office, sports, home, whatever RFID keys you have, and we’ll see what Flipper can read from a bank card.

Most RFID tags are passive tags with no internal power source. The chip inside is completely turned off until the tag is exposed to the reader’s electromagnetic field. As soon as the tag’s antenna comes into range, it begins to absorb the energy of the reader’s electromagnetic field, and the chip receives power. Then the chip turns on and starts exchanging data with the reader. It is worth noting that the antenna of the tag is tuned to a specific frequency, so the tag can only be activated when it is inside the corresponding electromagnetic field.
Externally, RFID tags can be very different: cards, both thick and thin, key chains, bracelets, coins, rings or even stickers. Judging by visuals alone, it’s almost impossible to tell which frequency or protocol a tag is running on.

Quite often, manufacturers use similar plastic cases for different types of RFID key fobs operating at different frequencies. Two completely similar tags can be completely different inside. This is something to consider when trying to discern the type of label you have. In this article, we will look at the two most popular types of RFID tags used in access control systems. Flipper Zero supports both of these frequencies.
There are many RFID protocols operating at other frequencies. UHF, for example, uses the range 840-960 MHz. They are used to track assets in warehouses, pay for toll roads, track wild animals during their migration, and more. These tags can be battery-powered and run from a few meters to kilometers. However, they are quite rare and you may not come across them unless you are specifically looking for them. We will omit them entirely for the purposes of this article.
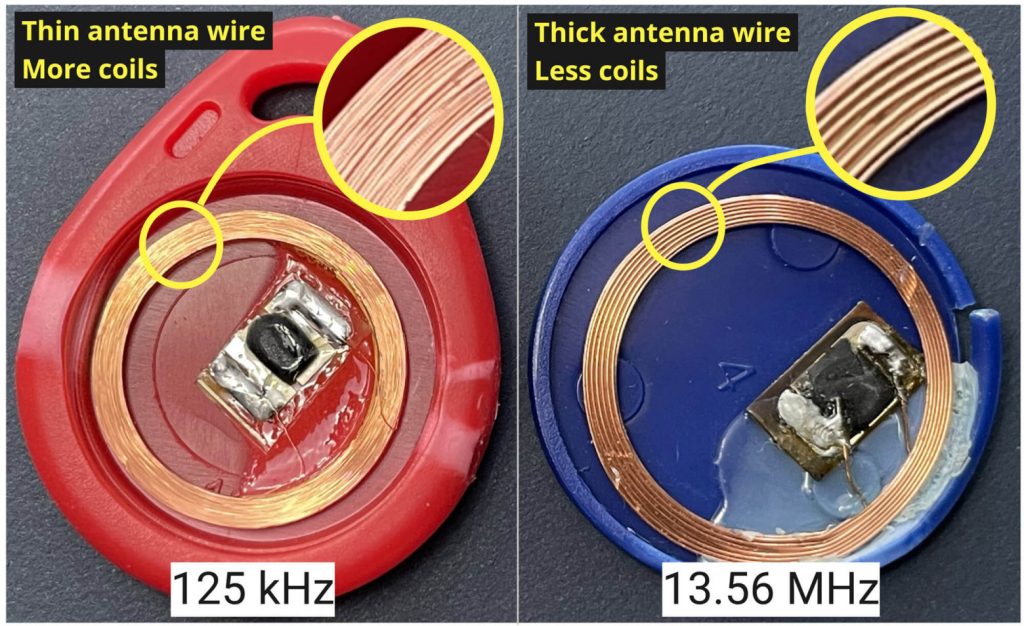
The easiest way to tell what band an RFID tag works on is to look at the antenna. Low-frequency tags (125 kHz) have an antenna made of very thin wire, literally thinner than a hair. But such antennas have a large number of turns, so such an antenna looks like a solid piece of metal. High-frequency cards (13.56 MHz) have significantly fewer thicker turns, with visible gaps between them.

You can shine a light on the RFID card to see the antenna inside. If the antenna has only a few large turns, it is most likely a high-frequency antenna. If the antenna looks like a solid piece of metal without gaps between the turns, then it is a low-frequency antenna.
Low-frequency tags are often used in systems that do not require a high level of security: building entrances, intercom keys, gym memberships, etc. Due to their greater range, they are convenient to use for paid parking: the driver does not need to bring the card close to the reader, as it is activated from a greater distance. At the same time, low-frequency tags are very primitive, they have a low data transfer rate. For this reason, it’s impossible to implement complex two-way data transfers for things like balance keeping and cryptography. Low-frequency tags transmit only their short identifier without any means of authentication.
High frequency tags are used for more complex reader-tag interactions when you need cryptography, large two-way data transfer, authentication, etc. They are usually found in bank cards, public transport and other secure passes.
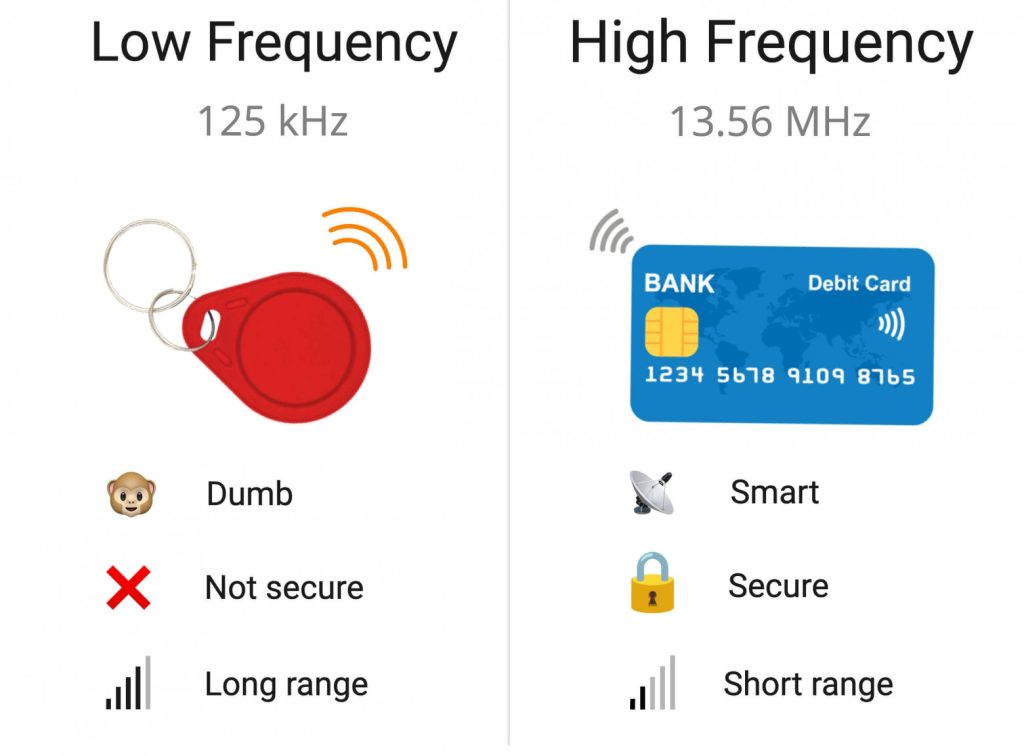
Wide Range – Lower frequency is converted to a larger range. There are EM-Marin and HID readers that work at a distance of up to a meter. They are often used in car parking lots.
Primitive Protocol – Due to low data rates, these tags can only transmit their short identifier. In most cases, the data is not authenticated and not protected in any way. As soon as the card is in range of the reader, it simply starts transmitting its ID.
Low level of security – these cards can be easily copied or even read from someone else’s pocket due to the primitiveness of the protocol.
Low range – High frequency cards are specially designed to be placed close to the reader. It also helps protect the card from unauthorized activity. The maximum read range we were able to achieve was about 15 cm, and that was with custom-made high-frequency readers.
Advanced Protocols – Data rates up to 424 Kbps enable complex protocols with full two-way data transfer. Which in turn enables cryptography, data transfer, etc.
High level of security – high-frequency contactless cards are in no way inferior to smart cards. There are cards that support cryptographically strong algorithms such as AES and implement asymmetric cryptography.

Flipper supports both high-frequency and low-frequency tags. To support both frequencies, we have developed a dual-band RFID antenna that is located at the bottom of the device.
For high-frequency protocols (NFC), a separate NFC controller (ST25R3916) is used. It takes care of everything related to hardware interaction with cards: reading and emulation. Low-frequency 125 kHz protocols are implemented in software via a configurable analog interface that works in conjunction with the MCU and allows read, write, and emulation.
[Video] RFID antenna inside Flipper Zero.
The upper part of the printed circuit board is protected by a ferromagnetic layer, which isolates the rest of the electronic components from interference and extends the operating range by reflecting the high-frequency field.
During assembly, the antennas are glued into the back panel of the Flipper. It connects to the printed circuit board using pogo pins. This greatly simplifies assembly as no UFL cables and connectors are used.
Low-frequency tags store a short identifier, only a couple of bytes long. The ID of the label is compared with the IDs stored in the database of the controller or intercom. However, the card will give its ID to anyone who asks once it’s powered up. Quite often the ID is printed on the card itself, so you can take a picture and enter it into Flipper manually.
EM-Marine – EM4100, EM4102. The most popular protocol in the CIS. Thanks to its simplicity and stability, it can be read from about a meter.
HID Prox II is a low frequency protocol introduced by HID Global. This protocol is more popular in Western countries. It is more complex, and cards and readers for this protocol are relatively expensive.
Indala is a very old low frequency protocol introduced by Motorola and later acquired by HID. You’ll find it less common in the wild compared to the previous two, as it’s becoming obsolete.
In fact, there are many more low-frequency protocols. But they all use the same modulation at the physical level and can be considered, one way or another, a variety of the above. At the time of writing, Flipper can read, store, emulate and write all three protocols. There may be others that are not supported by the Flipper firmware, but since the 125kHz subsystem is implemented in software, we may add them in the future.
[Video] Flipper reads EM-Marin tag
EM-Marin is the most common format that we have in the CIS. It is simple and has no copy protection. EM-Marin cards usually have EM4100 chips, but there are others. For example, you may have an EM4305 that can be rewritten as opposed to an EM4100.
To read a low-frequency card, go to Flipper 125 kHz RFID -> Read and place the tag on the back of the device. Flipper will attempt to determine the protocol and, if successful, will display it along with the card ID. Since Flipper tries all protocols at the same time, this takes some time. For example, it will take you a few seconds to read an Indala card.

The EM4100 unique code is 5 bytes long. Sometimes it can be found on the card itself. The unique code can be written in both decimal and hexadecimal. Flipper displays the code in hexadecimal, however EM-Marin cards usually only have the lower 3 bytes written, not the full 5-byte number. If there is no way to read them from the card, the other 2 bytes can be forced.
[Video] 125kHz RFID emulation to open electric door lock
To emulate an RFID tag, we need to go to the 125 kHz RFID —> Saved menu, select the required tag and click Emulate.
Some intercoms try to protect themselves from key duplication by sending a write command before reading. If the entry succeeds, this tag is considered fake. When Flipper emulates RFID, the reader cannot distinguish it from the original, so there are no such problems.
[Video] Flipper reads HID26 tag
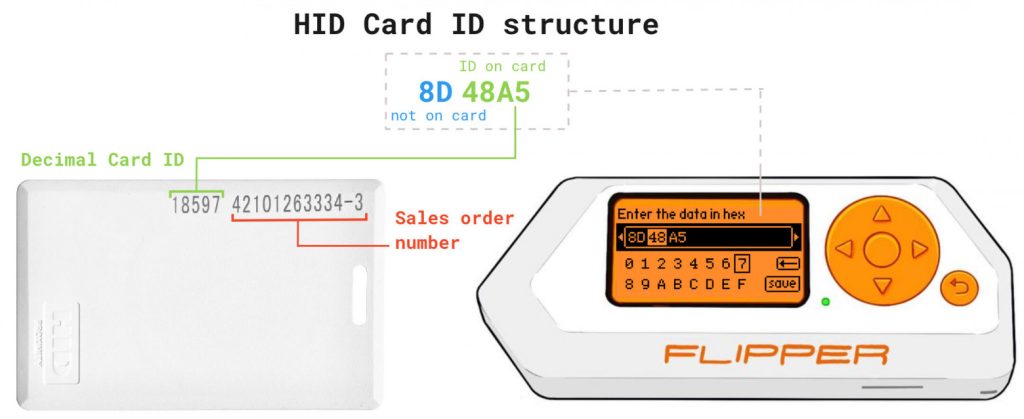
HID Global is the largest manufacturer of RFID devices in the world. They have several high-frequency and low-frequency RFID protocols. The most popular low-frequency HID protocol is the 26-bit H10301 (also known as HID26 or HID PROX II). The length of the unique code is 3 bytes (24 bits), and another 2 bits are used for parity checking (to ensure data integrity).
The numbers written on some HID26 cards are the sales order number and the card ID. You cannot determine all 3 bytes from this information alone, the card only has 2 bytes printed on it in decimal format. This is the card ID.
Flipper can only work with the HID26 protocol of the HID family. We plan to expand this list in the future. The HID26 is the most popular because it is compatible with most digital access control systems.
[Video] Flipper emulates a low-frequency map and opens a turnstile
Indala is an RFID protocol developed by Motorola and later acquired by HID. This is a very old protocol that you will not find in modern access control systems. Although it is rare, you can sometimes find it in the field. At the time of writing, Flipper works with the Indala I40134.
[Video] Flipper reads an Indala card
As with the HID26, cards using the Indala I40134 have a 3-byte unique code. Unfortunately, the Indala data structure is proprietary, and anyone wishing to support this protocol is forced to choose any byte order and how to interpret the signal at the hardware level.
All these protocols are so simple that the card ID can be entered manually without the original card. By having your card ID in text format, anyone who owns Flipper can enter it manually.
[Video] Entering Indala Card ID without the card itself
To add a card ID, go to the menu and select 125 kHz RFID —> Add manually, then the protocol and enter the ID. The added map will be saved to the SD card and can then be emulated or written to blank space.
There are custom blanks that support any of the three protocols mentioned above (EM-Marin, HID Prox, Indala). T5577 is the most popular type of blank card. To write an ID to a blank card, go to 125 kHz RFID —> Saved, select the desired key and click Write.
[Video] Recording on a blank T5577 card
13.56 MHz high-frequency labels are a set of standards and protocols. They are usually called NFC, but this is not always correct. The main set of protocols used at the physical and logical layers is ISO 14443. High-level protocols are based on it, as well as alternative standards (such as ISO 19092).
ISO 14443-A seems to be the most common implementation. It is used by almost all public transport and office fares, as well as bank cards.
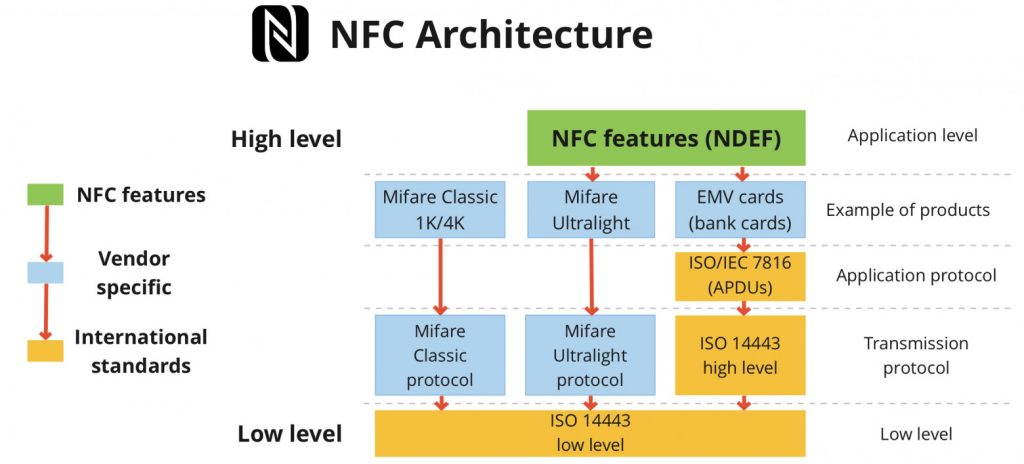
Simply put, the NFC architecture works like this: the transmission protocol is chosen by the card company and implemented based on the low-level standard ISO 14443. For example, NXP invented its own high-level transmission protocol called Mifare. But at a lower level, Mifare cards are based on the ISO 14443-A standard.
Flipper can interact with both the low-level ISO 14443 protocol and the Mifare Ultralight and EMV data transfer protocols used in bank cards. We are working on adding Mifare Classic and NFC NDEF support. A detailed look at the protocols and standards that make up NFC is worth a separate article that we plan to publish at a later date.
[Video] Reading a UID from a high-frequency tag of an unknown type
All ISO 14443-A-based high-frequency cards have a unique chip ID. It acts like the serial number of the card, like the MAC address of the network card. UIDs are usually 4 or 7 bytes long, but rarely can be as long as 10. UIDs are not secret, they are easy to read, sometimes even printed on the card itself.
There are many access control systems that rely on UIDs for authentication and access. Sometimes this happens even if the RFID tags support cryptography. This kind of abuse drops them down to dumb 125kHz cards in terms of security. Virtual cards (such as Apple Pay) use a dynamic UID to prevent phone owners from opening doors with their payment app.
[Video] iPhone generates a new UID every time Apple Pay is read
Since the UID is a low-level attribute, you may find yourself in a situation where the UID has already been read, but the high-level data transfer protocol is still unknown. You can read, emulate, and manually enter UIDs with Flipper for primitive readers that use UIDs for authorization.

In Flipper, the reading of 13.56 MHz tags can be divided into two parts:
Low Level Read – Only reads UID, SAK and ATQA. Flipper tries to guess the high-level protocol based on the data read from the card. You cannot be 100% sure as this is just a guess based on certain factors.
High-Level Read – Reads data from the card’s memory using a specific high-level protocol. This will be reading data on Mifare Ultralight, reading sectors from Mifare Classic or reading card attributes from PayPass/Apple Pay.
To use a specific high-level protocol when reading data, go to NFC —> Run special action and select the type of tag you want to read.
To try to guess the tag type and read the UID, go to NFC -> Read card. So far Flipper can only detect Mifare Ultralight and EMV bank card.
[Video] Reading data from Mifare Ultralight
Mifare is a family of contactless smart cards with several high-level protocols. The simplest of them is Mifare Ultralight. In its basic version, it has only 64 bytes of built-in flash memory and no cryptographic protection. Flipper can both read and emulate Mifare Ultralight cards. Such tags are often used as passes for access to offices, homes and public transport. Tickets for public transport in Moscow, for example, use Mifare Ultralight.
[Video] Reading data from a bank card
EMV (Europay, Mastercard and Visa) is an international set of bank card standards. Bank cards are now full-fledged smart cards with complex data exchange protocols and support for asymmetric encryption. Besides simply reading the UID, you can extract a lot more data from a bank card. You can get the full card number (16 digits on the front of the card), expiration date, and in some cases even the name of the owner along with a list of recent transactions.
Because the EMV standard can be implemented differently, the data that can be retrieved may vary from card to card. You cannot read the CVV this way (3 digits on the back of the card).
Bank cards are protected against replay attacks, so copying them with Flipper and then trying to emulate it to pay for something won’t work.

Compared to a plastic bank card, the virtual card in your phone provides less information and is safer for offline payments.
They don’t allow you to use the data you receive for online payments – a regular card can be used for Card-Not-Present (CNP) transactions, and sometimes you can pay online or over the phone. Intercepted virtual card data cannot be used in this way. After registering the card in Apple Pay, all payments go through a virtual token, and all transactions are cryptographically signed. Reading Apple Pay data results in the PAN number and expiration date of a virtual token, not the original physical card. Thus, if someone tries to use the data intercepted from the virtual card to make an online payment, such a payment will be rejected without a special signature.
They do not reveal the cardholder’s name – some contactless cards may transmit the cardholder’s name and recent transaction details. Virtual cards do not.
Bank card support in Flipper is implemented solely for the purpose of demonstrating a high-level protocol. We have no plans to expand this feature further. The security of contactless bank cards is high enough that you don’t have to worry about devices like Flipper being used to attack bank cards.