

In this instruction, we will tell you how to find a camera in a certain city (in our case, search for a camera in the Russian Federation or in the temporarily occupied territories) and get access to the camera. It helps track the movement of enemy troops and equipment using cameras in the regions. You can help Ukraine while sitting on the couch. Any information from CCTV cameras can be useful. The link to the appropriate software for searching and hacking CCTV cameras will be in the article. The instructions describe actions for scanning IP addresses and ports belonging to video surveillance cameras. To gain access to a camera or other equipment in the network, we need to know its address, login and password. The default login and password are very easy to find, depending on the manufacturer. Known, factory and default ones can be found on the Internet.
You can also find a dictionary with the most frequently used logins and passwords. The 4it.me and 2ip.ua resources will help you find bands outside the city. We will also introduce you to the VNC scanner GUI and KPortScan3 programs. They are used to quickly scan multiple IP ranges with a specified port. You can use Zenmap or Nmap to quickly search for a single range. It’s a single program, but Zenmap has a graphical skin. With the help of a specialized program for brute force – hikka, we will automatically detect active cameras. The next step is to select a login and password based on the built-in dictionaries. Hikka dictionaries can be personally edited using the text editor built into the operating system. We will automatically receive screenshots from successfully hacked cameras. They are in the directory with the program. The above-mentioned programs work under the Windows operating system. You can use the program masscan or Nmap to quickly find addresses under the Linux OS. In advance, we always recommend using a virtual machine and a double VPN for relatively safe use of the software listed below. Do not neglect your safety!
For a convenient search of IP address ranges, we recommend using https://4it.me/getlistip or https://2ip.ua/ru/services/information-service/location-ip On the website for search, we choose a city and get a list of addresses that we will use. For convenience, we advise you to save the received information in a text file.
A large number of different scanners can be used for a quick search in automatic mode from the Windows operating system. We will show you the example of two convenient small programs – KPortScan3 and VNC scanner. The advantages of these programs are a convenient and simple interface, the possibility of using a list of IP address ranges, and speed of operation.
Or find it yourself on the Internet. WARNING! Most of the specialized software on the Internet can contain malicious software or be detected by antivirus programs as conditionally dangerous. Choose wisely what to download and run. Always do this on isolated virtual machines.
We launch the program. If the antivirus complains about potentially dangerous software, we add it to the exception. Add a list of IP addresses to the selected window.
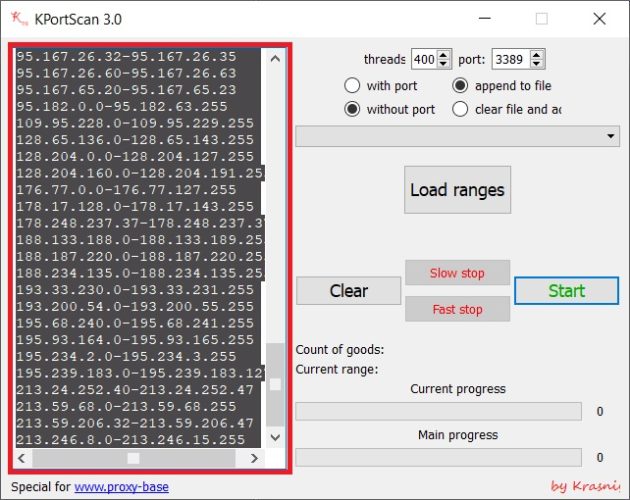
Select the port for scanning. Cameras can most often use ports: 8000, 8080, 8888, 554.
We can specify only 1 port in the scan program. By clicking without port, only the IP address without port will be recorded in the result file.
After choosing everything, press the Start button.
Note: even if there is a positive response according to the results of the scan, this does not mean that the camera is located on that port. It should also be noted that the port with the access page or RTSP stream may have been changed.
Based on the results of the scan, the program will give us the number of positive responses and automatically record the result in the results.txt file located in the directory with the program. Next, we will work with him. If you want to continue scanning with other ports, you can select append to file, and then the result of the next scan will be added to the results.txt file.
Enter the range of IP addresses in window 1.
In windows 2 and 3, we enter the camera ports (most often they are 8000, 8080 and 8888).
In window 4, select the country of scanning.
Press window 5 and wait for the scan to complete.
We will use the compiled version of the VNC scanner GUI for Windows. It should be noted that the version of this scanner is also available for Linux. But for Linux I recommend using masscan.
For example, the city of Dzhankoy:
The scanning process is as follows:
We are waiting for the end… The process can take a long time… It all depends on the number of IP addresses that need to be processed, the power of the machine and the speed of the Internet.
After the scan is finished, press the start button and MUST close the program window (only then will all data be saved). After that, the program will save the IРs.txt file in its folder (we need it later).
The next step is to use the hikka program, which will take screenshots of the detected cameras.
папка pics – these will be saved photo files from cameras in jpg format. The file name consists of the username, password, IP address of the camera and the number of cameras;
файл logins– logins for sorting;
файл passwords – passwords for sorting (we take logins and passwords in free access, or via the link);
файл hosts– range of ir addresses to search.
All files are opened and edited using a standard text editor. The photo shows two versions of hikka, but the files are the same.
For the hikka program to work, it is necessary to enter the range of IP addresses that the VNC program (range scanner) gave us in the hosts file. As I already mentioned, this is a text file IРs.txt. We copy the range from it and paste it into the hosts file in the hikka program folder. When everything is ready, run the executable file start.bat
The white line is a “dead” IP address;
Red line – the connection is established;
Green line – gaining access;
Blue line – getting a screenshot from a hacked camera!
We wait for the end of the scan (in the ideal case, the window will close, the work is complete. But most often it happens that the program hangs. If it hangs, then copy the last IP address, find it in the hosts file and delete everything above this IP address and run it again on scanning).
We wait for the end of the scan (in the ideal case, the window will close, the work is complete. But most often it happens that the program hangs. If it hangs, then copy the last IP address, find it in the hosts file and delete everything above this IP address and run it again on scanning).
After scanning all ranges, find screenshots of the cameras in the pics folder and send them to the official SBU bot https://t.me/stop_russian_war_bot, which they officially posted in their Telegram channels https://t.me/SBUkr/3762, in the bot, select the CyberFront section as in the photo below, or the mother’s hacker bot https://t.me://HackYourMom_reg_bot.
Glory to Ukraine!

